Stunning & Instant Business Equipments Overview
Explore our user-friendly map feature for a quick and complete view of your business. Easily track all essential information and operations, gaining valuable insights at a glance.
EasyShare Data with Customers
Simplify data-sharing with EasyShare! Promote transparency, improve connections and communicate better with your customers. It’s as easy as a click!
Multiple Business Management
Easily manage multiple businesses with our all-in-one solution. Optimize operations, simplify complexity and enhance your business management experience.
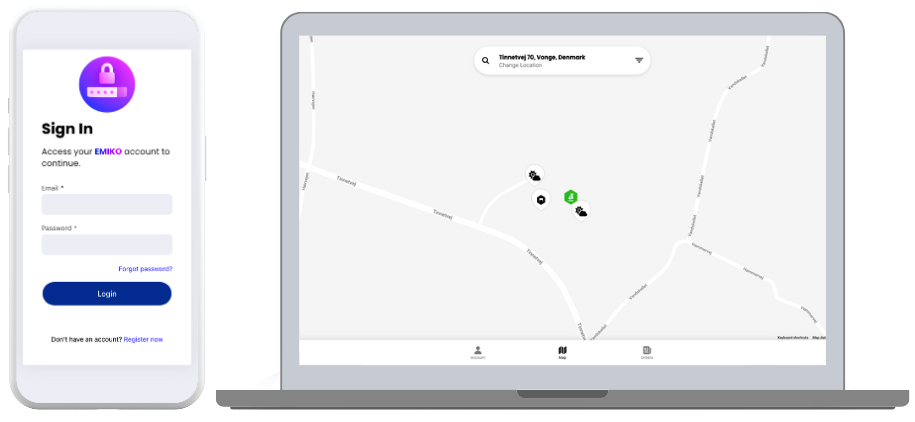
Cross-Platform Customer App
Engage with customers across various platforms, ensuring a unified and user-friendly experience. Simplify interactions, boost customer satisfaction and elevate your business presence.
Real-Time Usage Consumption
The app that puts real-time consumption data at your fingertips. Stay informed, optimize resources and take control with LiveUsage Insight!
Fast Customer Onboarding
Quick Equipment Access
Experience swift equipment access! Grant customers time-limited or permanent access to both private and public equipment.
Fast Customer Request Access
No more waiting in line or searching for business personnel. Customers can request access directly through the app and enjoy a smooth process.
Oeconomia API – ERP Solution
The Oeconomia API provides the advantage to optimize and integrate workflows by electronically transferring consumption data to your own financial system.

EMIKO Mapper
Get More with Upgrades: Subscription Tier Benefits
Unlock Business Flexibility
with Emiko Software
Quick Setup
Quick and easy onboarding with Emiko System.
Easy Migration
Expert assistance for a smooth Emiko Systems migration.
Endless Improvements
We have a team of experts who are constantly making improvements.
Custom Development
On-Demand Custom Development for a personalized experience.
Cross-Platform App
Unlock universal access – Your anytime, anywhere solution!
Fasten Release Cycles
Fast and Efficient Progress through Accelerated Releases.
NIS2 Compliance and
Security Protocols
Security Safety takes center stage in Emiko Systems, prioritizing the privacy of users and ensuring a secured and trustworthy environment for all interactions.